Are Your Vendors Exposing
You to Risk?
HITRUST TPRM Services provides greater confidence that your organization is doing everything possible to enhance data protection and minimize third-party risk. Our best-in-class managed services team further streamlines Third-Party Risk Management (TPRM) while helping you make better-informed risk decisions.
HITRUST TPRM Services
HITRUST TPRM Services are fully managed services offered by HITRUST.
They enable your organization to augment or completely outsource your vendor risk management. Our team provides a consistent, transparent assessment mechanism backed by HITRUST’s TPRM methodology.
Designed to improve TPRM efficiency and security and reduce costs, the HITRUST TPRM Services team
- Facilitates streamlined inherent risk tiering and scoring methodology
- Delivers automated classification of third-party vendors and suppliers, with recommendations for which assurance to request
- Provides reliable validation of third-party information practices against continuously updated controls
- Enables easier and more comprehensive comparison of your vendor population, facilitating risk remediation as needed
Our TPRM Services approach employs a six-step process to recommend the appropriate assurances to request from your vendors.
Third-Party
Pre-Qualification
Review vendor data access and assess impact.
Risk Triage
Evaluate and classify third parties based on risk factors.
Risk Assessment
Obtain and review assurance reports to accurately assess security and privacy risk.
Risk Mitigation
Identify gaps and implement Corrective Action Plans (CAPs) to reduce risk to an acceptable level.
Risk Evaluation
Determine remaining risk and prepare appropriate vendor qualification recommendations.
Third-Party Qualification
Based on risk tolerance, engage management to accept or reject any known third-party risk.
Inherent Risk Assessment
HITRUST's Inherent Risk Module enables organizations to assess risks in business relationships, segment vendors, and determine appropriate assurance levels.
This process is particularly useful for:
- Assessing new third parties with unknown risk profiles, such as potential vendors from an RFP or onboarding process
- Validating or challenging current vendors' risk tiers against an unbiased metric
- Ensuring risk assessment requests are thorough yet not burdensome
- Aligning risk factors between internal and external parties
- Obtaining additional data from vendors through customized questions
Risk Assurance Portfolio
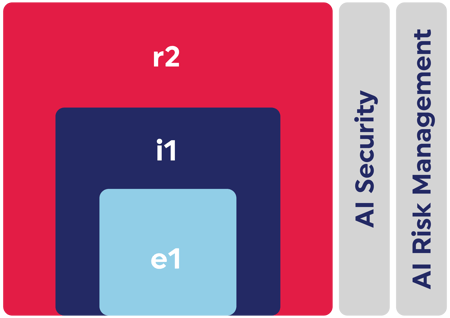
HITRUST’s scalable, flexible portfolio offers multiple assessment levels of assurance aligned with the risk profile, maturity, resources, and budget of your vendors.
e1 Self-Assessment
Your organization will determine the final assurance level for each vendor, but many start with an e1 Self-Assessment. This assessment focuses on essential information security controls curated by HITRUST from sources like CISA Cyber Essentials, Health Industry Cybersecurity Practices (HICP) for Small Healthcare Organizations, NIST 171’s Basic Requirements, and NIST IR 7621.

The e1 Self-Assessment is ideal for:
- Organizations with lower risk profiles
- Service providers and organizations with limited PII business processes (e.g., sales/marketing, call centers, brokers, auditors)
- Vendors in the RFP or onboarding process
- Third parties expanding services
- Business partners taking the first step toward higher certification levels
Higher Levels of Assurance
In addition to the e1 Self-Assessment, HITRUST offers e1, i1 or r2 Readiness or Validated Assessment (+Certification), an AI Assessment and Certification, and an AI Risk Management Assessment.

Which assessment type is
right for your organization?
HITRUST e1 - 1-year Validated Assessment: Foundational Cybersecurity
The e1 assessment and certification is ideal for startups and companies with limited risk profiles or less complexity. It allows for an entry-level validated assessment and certification based on 44 foundational security controls. Organizations can also build upon these controls as a step toward attaining the more comprehensive i1 or r2 certifications.
HITRUST i1 - 1-year Validated Assessment: Leading Security Practices
The i1 assessment and certification is a good fit for organizations with robust information security programs already in place that are ready to demonstrate leading security practices. The i1 offers a more comprehensive assurance than the e1, with more controls included. Work done to attain an active i1 certification can be applied toward attaining an r2 certification.
HITRUST r2 - 2-year Validated Assessment: Expanded Practices
The r2 assessment and certification is best suited for organizations that need to demonstrate regulatory compliance with authoritative sources like HIPAA, the NIST Cybersecurity Framework, and dozens of others or that require expanded tailoring of controls based on other identified risk factors. It is the most comprehensive and robust HITRUST assessment.
AI Security Assessment and Certification
The AI Security Assessment is designed to provide AI platform and service providers with relevant, prescriptive, practical security controls and methodology to confidently adopt and secure AI technologies. It supports shared responsibility inheritance and when paired with an e1, i1, or r2, enables organizations to address multiple compliance needs within a streamlined solution.

AI Risk Management Assessment
The HITRUST AI Risk Management Assessment offers detailed insights, based on 51 relevant and practical AI risk management controls. Harmonized with ISO 23894 and NIST AI RMF, this assessment provides a single, efficient control specification that allows organizations to understand and report on their performance in ISO and NIST terms.

